archive.today and archive.ph (also .is, .md, .fo, .li, .vn) could be Russian assets.
- Posts
- 10
- Comments
- 730
- Joined
- 9 mo. ago
- Posts
- 10
- Comments
- 730
- Joined
- 9 mo. ago
Welcome to the rest of your life. There'll be a lot more of this.
"Well, son, a funny thing about regret isThat it's better to regret something you have doneThan to regret something you haven't done.""And by the way, if you see your mom this weekendWould you be sure and tell her
Here in the dark North I take - during winter only - 50µg daily. I never take it before going to sleep, but tbh I have no idea if it would even make a difference. Sometimes I feel a bit of an effect - like eating something rich in Vitamin C after a day without vitamins. But all in all, I don't think this alone will improve your mood.
I hesitate to explain.
I had to check if this really is what OP describes. Yes, it is:
Argh! Order a deathtrap from AliExpress!(OK, to be fair, I got an electric shock from one of these once - hand made by my landlord - and luckily I'm still alive, but really, don't)If crowdsec works for you thats great but also its a corporate product
It's also fully FLOSS with dozens of contributors (not to speak of the community-driven blocklists). If they make money with it, great.
not exactly a pure self hosted solution.
Why? I host it, I run it. It's even in Debian Stable repos, but I choose their own more up-to-date ones.
Allow me to expand on the problem I was having. It wasnt just that I was getting a knock or two, its that I was getting 40 knocks every few seconds scraping every page and searching for a bunch that didnt exist that would allow exploit points in unsecured production vps systems.
- Again, a properly set up WAF will deal with this pronto
- You should not have exploit points in unsecured production systems, full stop.
On a computational level the constant network activity of bytes from webpage, zip files and images downloaded from scrapers pollutes traffic. Anubis stops this by trapping them in a landing page that transmits very little information from the server side.
- And instead you leave the computations to your clients. Which becomes a problem on slow hardware.
- Again, with a properly set up WAF there's no "traffic pollution" or "downloading of zip files".
Anubis uses a weighted priority which grades how legit a browser client is.
And apart from the user agent and a few other responses, all of which are easily spoofed, this means "do some javascript stuff on the local client" (there's a link to an article here somewhere that explains this well) which will eat resources on the client's machine, which becomes a real pita on e.g. smartphones.
Also, I use one of those less-than-legit, weird and non-regular browsers, and I am being punished by tools like this.
All the self hosters in my internet circle started adopting anubis so I wanted to try it. Anubis was relatively plug and play with prebuilt packages
edit: I feel like this part of OP's argument needs to be pointed out, it explains so much:
All the self hosters in my internet circle started adopting anubis so I wanted to try it. Anubis was relatively plug and play with prebuilt packages
- JumpNSFW Removed
debian trixie dns config rant
IMO this is largely Debian-specific: this distro seems to hold backward comaptibility in very high regard, so any problem is bound to have a multitude of solutions. In addition, the Debian Wiki is not as well maintained as you-know-whose.
I see nothing untoward here.
Except maybe that last sentence, what "s" are you talking about (fwiw, the man page that comes with an installed package should™ be the ultimate authority)?
I guess it would.
OTOH it's always one of the first things I disable on my phone. That being mandatory would piss me off.
In most laptop web cams, the little LEDs are part of the hardware/firmware modules.
At the time of commenting, this post is 8h old. I read all the top comments, many of them critical of Anubis.
I run a small website and don't have problems with bots. Of course I know what a DDOS is - maybe that's the only use case where something like Anubis would help, instead of the strictly server-side solution I deploy?
I use CrowdSec (it seems to work with caddy btw). It took a little setting up, but it does the job.(I think it's quite similar to fail2ban in what it does, plus community-updated blocklists)
Am I missing something here? Why wouldn't that be enough? Why do I need to heckle my visitors?
Despite all that I still had a problem with bots knocking on my ports spamming my logs.
By the time Anubis gets to work, the knocking already happened so I don't really understand this argument.
If the system is set up to reject a certain type of requests, these are microsecond transactions of no (DDOS exception) harm.
it's mentioned in this article
That was my first thought. And how many people have done this already? It's way too easy to take pictures of people while pretending to just be on your phone. They should introduce a little red LED when the camera is on, at the very least.
There was (early 1900s) a cartoon series about a guy having weird dreams every time they ate a grilled (?) cheese sandwhich before going to sleep.
Disclaimer: this is not really about code, but about using IT in my non-IT workplace and I realized this just yesterday. A rant.
I work in the social sector. Our boss seems to have slipped into position sideways (they did not do our work for a significant amount of time before).
I got zero onboarding when I started working there; everything I know about the organisational ins and outs I learned by asking my colleagues.
The boss seems to actively want to not inform me of things, i.e. even if I ask about something they reply in the most cursory manner or immediately refer me to somebody else. I have no idea why they do it, my guess is that they sense that they're woefully inadequate for the job, plus me being much older triggers insecurities?
For example, when I could not log into an app to see my future shifts, I asked the boss about it first but they immediately refered me to tech support. Calling them, after a while we found out that the boss had mistyped my name. Then I could log in.
Last week I was sick and waited til Sunday noon to check this week's shifts - but again I couldn't log in. The boss answered neither phone nor email. Fair enough I guess, on a sunday. Thankfully tech support was working and after a long while we found out that the app for checking my shifts only allows log-ins from within the workplace network, not the open web.
I almost missed my monday shift because of that. Boss calls me, enraged. I explained the situation. They clearly did not know that the app only allows log-ins from within the workplace network.
All my coleagues tentatively/silently agree that this boss is useless. How do we keep the workplace running, and why is it me who is left in the dark? Turns out they have a Whatsapp group. I don't use Whatsapp. They asked me repeatedly and urgently to join.
tl;dr: this workplace would fall apart if people wouldn't communicate through Whatsapp instead of official channels
secondary definition breakfast table
...and who put them there in the first place.
Yeah, the whole thing is pretty fucked up. The world's societies & systems need a complete overhaul. Doesn't sound likely, does it?
Yes, all this shit is still happening while the world is looking elsewhere. China is also neocolonialistically active on the African continent, and I'm guessing the USA as well (still, despite MAGA).
I was wondering what happened to Wagner after Prigodzin died. Wrt Africa, it's now the MoD's Africa Corps.
They are continuing where Wagner left and if anybody ever tells you that Wagner is "not active in Africa anymore", that's the truth behind that.
How the Query Was Made
The evaluated participant directory of WhatsApp must fundamentally be open to WhatsApp users. They need to know who they can reach via the app. This is usually done by matching the smartphone address book. However, this does not require everyone to be able to access the user directory without limitation -- but that was exactly the case.
As Gabriel Gegenhuber (University of Vienna), Philipp Frenzel (SBA Research), Maximilian Günther, Johanna Ullrich, and Aljosha Judmayer (all Uni Wien) discovered, Meta allowed the matching of 7,000 phone numbers per second per instance using the XMP protocol, including the download of the respective device list. Profile data and key downloads were slightly slower at 3,000 and 2,000 per second, respectively. However, the profile photos were on an HTTP server that delivered 5,500 high-resolution images per second within the project.
The researchers made sure not to obscure their requests. They used the same static IP address for their queries, which was identifiable as belonging to the University of Vienna through the abuse contact data and whose administrator was reachable. Contact attempts to WhatsApp clients or interception of messages were not part of the procedure. The XMP queries generally ran with a maximum of five parallel threads and 50,000 data records per query, so as not to overload the infrastructure.
The researchers used the software whatsmeow for this purpose. This is an independent open-source implementation of WhatsApp. The parameters of the server interfaces (API) have been reverse-engineered for whatsmeow.
For photo downloads, however, the Viennese used 1,000 parallel threads, and for a short-term attempt, even 10,000. There were no reactions from the Meta servers or abuse complaints. The data company apparently refrained from monitoring. The collected photos and phone numbers were deleted by the scientists after the evaluation was completed.
Austria has 500 Billion Possible Mobile Numbers
One challenge was defining the number range to be scraped. The number of possible mobile phone numbers is enormous. Not only are the number ranges different in each country, but the length of the phone number can also vary within a country. Example Austria: The “area code” is followed by the subscriber identification, which can be seven to 13 digits long. It is not uncommon for a line to have more than one phone number.
This results in more than 511 billion possible mobile numbers for Austria alone. In Indonesia, there are still 89 billion. Google maintains with libphonenumber a public library for formatting and validating international phone numbers. At the time of the queries, it contained a good 646 billion phone numbers—the majority of them from Austria. Scraping this would have taken about a year.
As trained Austrians, however, the researchers knew to exclude certain number blocks because they are not used or hardly used in practice. Conversely, according to libphonenumber, there were surprisingly few number possibilities in Mexico and Brazil. It turned out that the number system had recently been reformed; numbers according to the old scheme were removed from libphonenumber, although they are still in circulation and valid.
After corresponding adaptations, the group finally defined a space of a good 63 billion phone numbers. In it, they found 3,546,479,731 WhatsApp accounts from 245 countries and territories. The actual number could be slightly higher, as it is possible that not all possible number ranges were captured in all area codes. In addition, satellite phone area codes (e.g., +870, +881) and special area codes like +800 were excluded. If network operators used their number blocks more extensively and assigned phone numbers randomly, scraping the number ranges would be more difficult for researchers as well as for spammers.
Statistical Delicacies
The most WhatsApp users, not surprisingly, are in India, with around 749 million. This means there are about 51 WhatsApp accounts per 100 Indians. There are over 200 million accounts in Indonesia and Brazil, and more than 100 million each in the USA, Russia, and Mexico. Per 100 inhabitants, this means 99 in Mexico and Brazil, 91 in Russia, but only 40 accounts in the USA.
In 32 regions, there are more than 100 accounts per 100 inhabitants, especially Monaco with 480. Countries in the Middle East and geographically small areas like Hong Kong, Sint Maarten, Singapore, Luxembourg, or the Turks and Caicos Islands predominate, but Chile, Malaysia, and the Netherlands also have more than 100 percent penetration. In the DACH region, Germany has 74.6 million WhatsApp accounts (88 per 100 inhabitants), Austria 7.9 million (86), Switzerland 8.4 million (95), and Liechtenstein 16,760 (43).
WhatsApp's market penetration is below five percent in Eritrea, Tokelau, Japan, South Korea, Ethiopia, Madagascar, Niue, Tuvalu, and Vietnam, as well as in three countries that completely ban the messenger (North Korea, China, Myanmar). In Japan, South Korea, and Vietnam, local messaging apps dominate the market. Regionally strong competitors explain WhatsApp's relative weakness in several countries. For example, Meta's offering only reaches 37 percent in Greece because Viber is the dominant player there.
Many Business Accounts in Africa
In no country did the researchers observe declining user numbers in the period from December 2024 to March 2025. They collected churn rates for Belgium, India, Iran, and the USA. The differences are significant. In Belgium, less than one percent of WhatsApp accounts disappeared monthly, while in the USA it was 3.6 to 4.3 percent, with Iran and India in between.
There are significant differences in the use of the profile picture function. It is extremely popular in Africa, where usually two-thirds to four-fifths set a picture. In the DACH region, Austria leads with 60 percent, followed by Switzerland with 58, Liechtenstein with 55, and Germany with 51 percent.
In some countries, there are surprisingly many business accounts: in Sierra Leone and Burundi, more than a third of all WhatsApp accounts fall into this category. In general, their share is high in Africa, but also in Haiti, the United Arab Emirates, Pakistan, Afghanistan, and Qatar; it is over 20 percent.
This is likely due to social customs, as Meta does not control whether an account is actually used for business. You just have to install the business version of the app. In Germany and Austria, two percent of users have done this; in Switzerland and Liechtenstein, three percent. Globally, it's nine percent.
Android vs. iOS
Since the WhatsApp application is implemented differently in Android and iOS, the Austrians were also able to gain insights into the market shares of these operating systems among WhatsApp users. Tendentially, the data available to heise online shows that the Android market share is significantly higher in poorer countries. Only in about half of the recorded countries does Apple's iOS reach over 20 percent. Worldwide, 81 percent of WhatsApp accounts are on Android.
Taking those regions where WhatsApp has at least a five percent market share and at least one million users, there are ten where iOS accounts for 51 percent or more: the USA, Denmark, and Australia lead with two-thirds iPhones each, followed by Canada, Norway, Sweden, Taiwan, Great Britain, Switzerland, and New Zealand.
Android and iOS are balanced in Luxembourg, Mongolia, and Hong Kong. In the two largest markets, India and Indonesia, Android dominates with well over 90 percent. This also applies to India's neighbors Bangladesh and Pakistan. In Germany and Austria, 58 and 59 percent are Android, respectively, while in Switzerland and Liechtenstein it is only 43 and 41 percent.
Recommendations
The research group published their findings on Tuesday under the title “Hey there! You are using WhatsApp: Enumerating Three Billion Accounts for Security and Privacy.” The paper has been accepted for the NDSS 2026 (Network and Distributed System Security) conference. It contains only one piece of advice for privacy-conscious WhatsApp users: they should reconsider their profile photo and info field. Due to the EU's Digital Markets Act, it may become possible in the European Economic Area to network alternative messenger systems with WhatsApp without directly using WhatsApp servers.
For Meta, they have more recommendations: limiting server queries (rate limiting), encrypting profile photos and info fields so that only confirmed contacts have access, and a uniform code base for different operating systems to provide attackers with less side-channel information. Once again, Signal is leading the way: the current beta already encrypts profile information.
Meta Platforms Reacts
An update to the Android app from October is intended to prevent keys from another account previously used on the device from being reused when a new WhatsApp account is created. In addition, WhatsApp servers no longer reveal timestamps for profile pictures. There is also now a restriction on the number of queries for profile pictures and info fields, except for business profile queries.
Meta has recently been trying to counter the mass matching of phone numbers by using machine learning and a lifetime limit on the maximum number of queries made by a WhatsApp account. This is intended to deter scrapers but not restrict normal users.
There are no CVE numbers for the problems discovered, as Meta generally does not apply for them for server problems. The data company considers the faulty reuse of keys when creating a new account on a device previously used for WhatsApp to be not serious enough.
Oletko varma että sinulla on maksumuuri siinä? Ei minulla (Uusimaa, Firefox).
Tässä koko artikkeli:
The entire member directory of WhatsApp was available online unprotected for retrieval. Austrian researchers were therefore able to download all phone numbers and other profile data—including public keys—without encountering any obstacles. They found more than 3.5 billion accounts. Measured by the number of people affected, this is likely the largest data leak of all time. Part of the research group has already dealt with WhatsApp several times and, for example, determined what WhatsApp reveals despite encryption and discovered how an attacker can downgrade WhatsApp encryption. Nevertheless, WhatsApp operator Meta Platforms turned a deaf ear to the new research findings for a year.
“Well, scientists now know a lot of phone numbers,” the responsible parties might have thought, “So what?” Repeated warnings submitted by the group from the University of Vienna and Austrian SBA Research to WhatsApp starting in September 2024 were acknowledged with confirmations of receipt but soon filed away. Only when the researchers submitted a draft of their paper twice and its uncoordinated publication was imminent did Meta wake up: a surprising amount can be read from the data, and for some users, it can be life-threatening.
First, there is information that is sensitive to Meta Platforms itself, for competitive and regulatory reasons: how many WhatsApp users are there in which country, how are they distributed across Android and iOS, how many are business accounts, what is the churn rate (customer attrition), and where are there obvious large-scale fraud centers. And then there are several classes of data that can be uncomfortable to life-threatening for users -- even though the researchers did not transmit any data packets to or from end devices (but only to WhatsApp servers) and did not intercept any content or metadata from WhatsApp communication.
Update 19.11.2025, 14:29 Uhr
Meta classifies the researchers' approach as "scraping" and points out that the data gathered has been securely deleted. "We have found no evidence of malicious actors abusing this vector" and private chats haven't been compromised, the company said in a statement provided to heise online.
"This collaboration successfully identified a novel enumeration technique that surpassed our intended limits, allowing the researchers to scrape basic publicly available information.We had already been working on industry-leading anti-scraping systems, and this study was instrumental in stress-testing and confirming the immediate efficacy of these new defenses.", says Nitin Gupta, VP of Engineering at Whatsapp. "As a reminder, user messages remained private and secure thanks to WhatsApp’s default end-to-end encryption, and no non-public data was accessible to the researchers."
WhatsApp Ban Ineffective
As of December 2024, WhatsApp was banned in the People's Republic of China, Iran, Myanmar, and North Korea. Nevertheless, the researchers found 2.3 million active WhatsApp accounts in China, 60 million in Iran, 1.6 million in Myanmar, and five (5) in North Korea at that time. This handful might have been set up by the state apparatus itself, but for residents of China and Myanmar, it is highly risky if authorities get wind of illegal WhatsApp use. And this happens easily when the entire number range can be queried quickly.
The 60 million WhatsApp accounts with Iranian phone numbers statistically corresponded to two-thirds of the population. The ban was obviously not effective there, and it was lifted on Christmas Eve 2024. Three months later, there were already 67 million Iranian accounts. The number of those using the same WhatsApp account on more than one device has increased significantly. During the ban, this was apparently too risky, but if WhatsApp is not illegal, one might want to use it on their work computer as well.
Profile Pictures and Info Field
Approximately 30 percent of users have entered something in the “Info” field of their profile, and some reveal a lot: political views, sexual or religious orientation, confessions of drug abuse are found there, as are drug dealers who advertise their product range in this very field. Beyond that, the Vienna researchers found information about the user's workplace, up to hyperlinks to profiles on social networks, on Tinder or OnlyFans. Email addresses were of course included, including from domains like bund.de, state.gov, and various from the .mil zone. This is a feast for doxxers and other attackers, but also for spammers and simple fraudsters.
In addition, WhatsApp revealed the time of the most recent change—not only of the info field but also of profile photos, which 57 percent of all WhatsApp users worldwide have uploaded and defined as visible to everyone, including US government officials. For the North American area code +1, the researchers downloaded all 77 million profile pictures visible to everyone—a proud 3.8 terabytes in total. In a random sample of half a million images drawn from this, a facial recognition routine found a human face in two-thirds of cases. The easy accessibility of the photos would therefore have allowed the compilation of a database that, through facial recognition, often leads to the phone number and vice versa. Even profile pictures without faces can be talkative: sometimes car license plates, street signs, or landmarks are depicted.
Further information is provided by the display of how many devices are registered under a WhatsApp account (up to five). From the continuously assigned IDs, it can be inferred whether these additionally used devices are frequently changed or remain stable.
Key Collisions
The research group also examined the public keys of all WhatsApp accounts. First, the good news: In the entire data mountain, there were only two invalid signatures. But unfortunately, there were 2.3 million keys that appeared on multiple devices. This should not happen, as it allows third parties to decrypt WhatsApp content or assume someone else's identity.
The majority of key copies (but not all) can be traced back to the lack of reissuance of a profile key when changing the phone number. This is not an IT security problem in the narrow sense, but a data protection problem because it allows the new phone number of a target person to be determined despite changing the phone number. This may undermine the purpose of changing the number. Therefore, anyone who changes their number due to danger from an oppressive regime, organized criminals, or an experienced intimate partner should also discard their WhatsApp account and, if necessary, open a new one.
Additionally, the end device should also be changed. The Vienna scientists have found that WhatsApp sometimes reuses keys if you log out of WhatsApp on a phone and then open a new WhatsApp account on the same device with a new phone number. This is a security flaw that Meta is now trying to address.
These three keys WhatsApp needs
In asynchronous communication, as is typical for WhatsApp, participants are not necessarily online at the same time; in such a case, direct negotiation of a key pair for encrypted communication fails. The Signal protocol, which is also the basis for WhatsApp in a variant, solves this problem by proactively uploading one-time public keys to the server. These are available for third parties to retrieve.
As a result, messages are encrypted end-to-end three times: with the static identity key pair, the signed pre-key pair exchanged approximately monthly (Prekey), which applies to exactly one conversation combination between two or more participants, and with the key pair valid for only a single message (for Perfect Forward Secrecy, PFS). PFS is intended to prevent other messages from being decrypted even if a key is compromised. Only someone who cracks all three keys can decrypt an intercepted message.
Indications of Fraud Centers
Some key reuse discovered cannot be explained by changing phone numbers—especially when, in addition to the profile key, the other two keys are also reused. One-time keys for individual messages are only supposed to be used once. Here, the researchers report clusters in Myanmar and Nigeria. There are even accounts where all three keys are the same and all three are reused.
Theoretically, this could be explained using a poorly made alternative WhatsApp client, which is popular in certain parts of the world. More likely, it is an indication of division of labor fraud, as often occurs via WhatsApp, for example through alleged wealth with cryptocurrency bets or by feigning great love. If the WhatsApp keys are intentionally the same, multiple perpetrators can share the same WhatsApp identity and thus work on a victim more efficiently, around the clock, without arousing suspicion through changing phone numbers. Conversely, perpetrators could use the same end device with new phone numbers to bypass blocklists.
Curious is a two-digit number of WhatsApp accounts where not only all three keys were identical and reused, but where the researchers were able to find out the private key: it consisted only of zeros. The reason is not clear; possibly the random number generator of the WhatsApp client used by these users is broken, whether intentionally or not.
Incidentally, the continuous identifier of the one-time keys could also be used to infer the age of the end device and/or the intensity of WhatsApp usage. This allows Meta and attackers to identify particularly popular accounts.
Suomi @sopuli.xyz WhatsApp, ChatControl yms
No Stupid Questions @lemmy.world When kids come trick-or-treating, what happens if I choose trick?
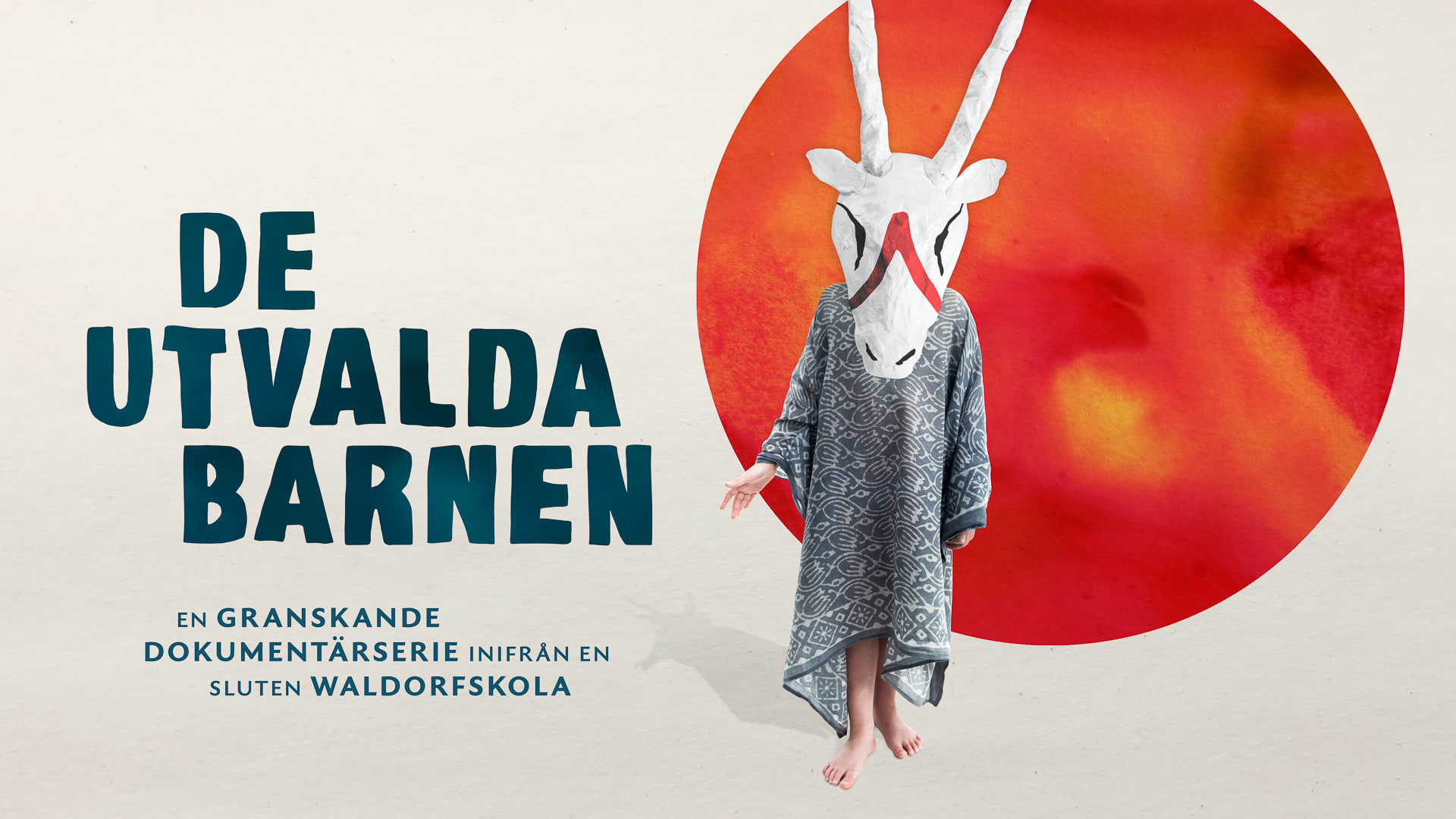
Suomi @sopuli.xyz Valitut lapset (dokkari Järnan Steinerkoulun oudosta historiasta)
Selfhosted @lemmy.world Safest CalDAV/CardDAV server
Privacy @lemmy.ml “archive.today” sends user data to Russia
Programming @beehaw.org Trying to recreate a version control system for my music collection, with one crucial difference ... 🤯
Linux @lemmy.ml Trying to recreate a version control system for my music collection, with one crucial difference ... 🤯
Asklemmy @lemmy.ml Does an Influx of Former Reddit Users create a Shift in Athmosphere?
Selfhosted @lemmy.world Which Static Blog Generator: blag, Jekyll, Hugo, Lektor, Pelican, staticsite?
Suomi @sopuli.xyz "Piraattikirje" Helsinkiläiseltä asianajotoimistolta

I asked three 5-year-old girls what they playing, they answered K-pop demon hunters. Each of them had a different garish hair color (represented by colorful beanies). That's about all I know about K-Pop Demon Hunters.